The IT for Learning Department has developed an automated process for reviewing suspicious email sent to spam@sd61.bc.ca. This procedure helps us review reported emails more efficiently, and act quickly in cases where the messages are proven to be dangerous. Your participation is critical in helping to keep the District’s digital environment safe.
Support Requests
Email you forward to spam@sd61.bc.ca is automatically scanned for malware and harmful links, but it is not individually assessed by ITL Support Staff. If you receive an email and would like support to determine its legitimacy you will need to contact helpdesk first, rather than forwarding the email to spam.
How To Forward
There are different ways to send a message onto another email address. To ensure that all the relevant details (including the email address and all attachments) get sent to Spam for analysis please forward the message using one of these methods:
Outlook Web 365

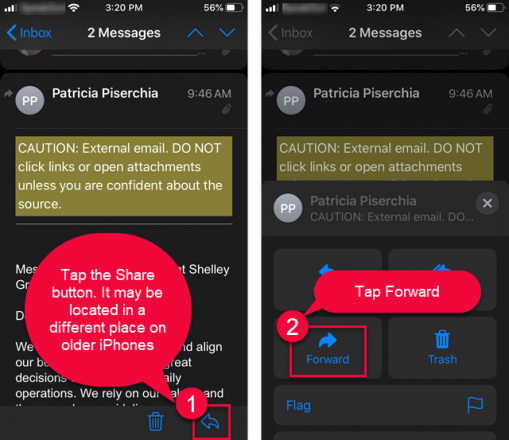
iPhones
What does suspicious email look like?
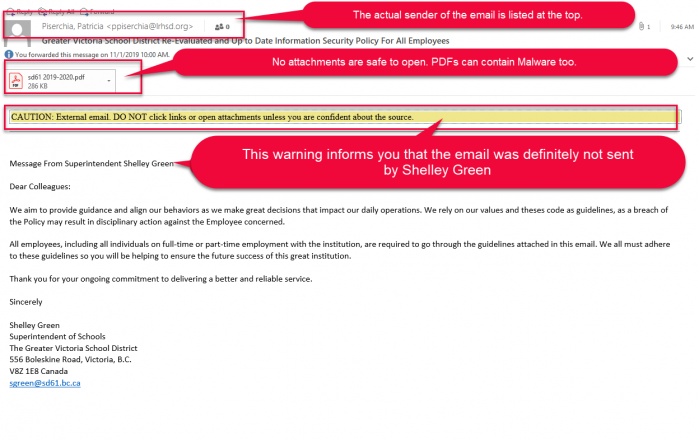
Malicious emails can take many forms and serve various objectives. It can seek credentials, inject malware, or perform other harmful functions. The following illustration does not begin to cover all these possibilities, but merely offers a snapshot of a recent, real-life incident in our district:
Analysis
Who is the Sender?
The recently added CAUTION label indicates that this message has not been sent from the superintendent—despite the contents of the email. It clearly demonstrates that the message is fraudulent. No email sent from district leadership, or any other employee will ever have this warning label attached. On Outlook and Outlook Web the true sender is the untrusted source listed at the top of the message.
What other clues are there?
There are other indications that this email is suspicious, beyond the warning. The threatening call to action “a breach of the Policy may result in disciplinary action against the Employee” strays from the kind of tone that one would expect of an email that has not been preceded by a more moderately worded message. The aggressive pitch is a tactic. Phishers know they have a limited amount of time to get a response before their ruse is discovered and measures are taken to counter it. When you are being rushed into a decision by threats, especially if it is supposedly coming from the district, check the tone. We do not issue threats.
I am curious, can I open the attachment?
Staff do sometimes receive valid outside emails that include attachments. But because attachments (including PDFs) can contain malicious elements it is always advisable to pay attention to the contents of the email and ensure it has come from a known sender before opening attachments. In this example the PDF contains a link to a site where your SD61 credentials are sought. This was a targeted attack against several school districts in our province. There were no nefarious elements within the PDF beyond the link. But that is not always the case. Given how questionable the sender is, and the fishy nature of the message one would be wise not to open this attachment, and instead forward the message directly to spam@sd61.bc.ca as soon as possible. However, if you believe the email may contain important information from a community partner or parent, and you want support to determine if it may be valid, contact helpdesk for assistance.