
What is Spoofing?
The word spoof is often used to describe satirical, goofball comedy films that, on the surface, pose as legitimate versions of a more serious genre. The classic movie “Airplane” for example, is a spoof of the Disaster/Thriller films that were popular in the 1970s. “This is Spinal Tap” is an early example of a mockumentary—i.e. a comedy posing as a documentary—about a fictional heavy metal band; “Best in Show” is another excellent mockumentary about a dog show. The “Scary Movie” series satirizes the Horror genre.
In the cyber-security world the term “spoofing” refers to a tactic where criminals pose as a legitimate, trust-worthy entity in order to steal valuable information, or request funds from unsuspecting victims. Spoofing attacks range in scope and sophistication, but the ones that pose the greatest threat to the Greater Victoria School District and its staff tend to come through email.
How do Spoofing emails work?
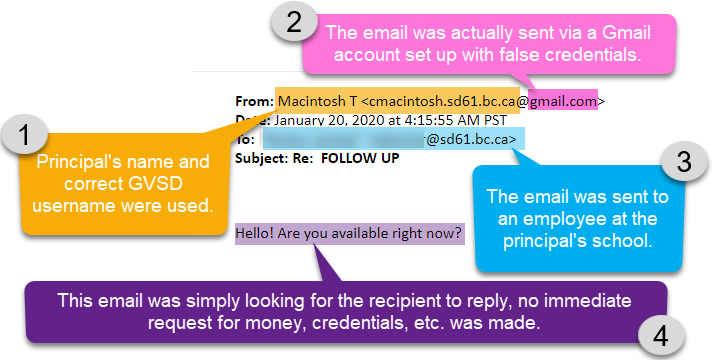
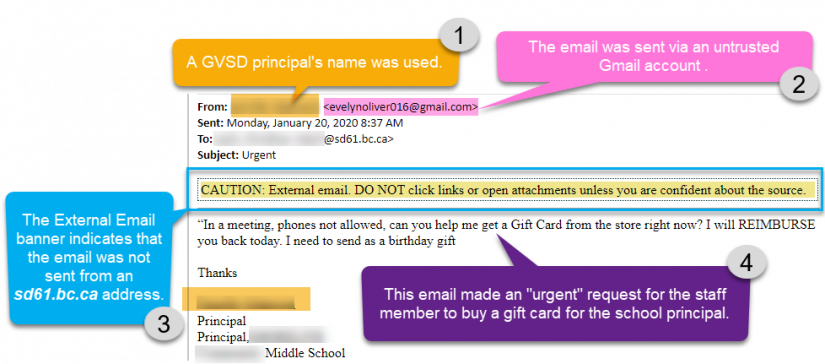
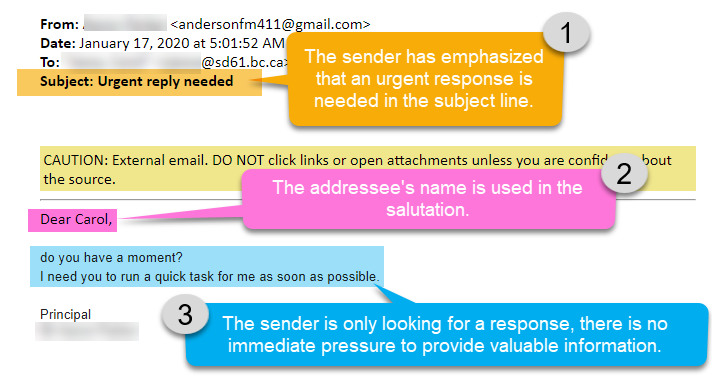
There is no single method for these types of scams, but typically spoofers gather a bit of intelligence about their target, and use a name the person knows, or a company/agency they may have dealings with, to deceive them. In the last month several perceptive District employees have reported spoofing incidents where criminals have tried to fool them by posing as principals of their school. The scammers used publicly available information—probably taken from our GVSD school websites—to learn the name of the principal and the employee’s GVSD email address. Here are three examples, taken from the GVSD’s spam@sd61.bc.ca inbox.
Example #1
Example #2
Example #3
What do Spoofers want?
It may not be obvious at first what the scammer is after. In the examples above only one immediately made a request for a tangible good. The other messages were brief, and only asked the user to please respond. A response probably would have generated another email from the scammer who eventually may have asked the user to:
- reveal their username/password
- open a malicious file posing as a legitimate document or link
- perform other action(s) that would have furthered the scammer’s criminal aims.
Are Spoofing emails always easy to identify and avoid?
No. Sometimes scammers gain access to real user email accounts via a successful phishing campaign, or pose as a representative of a bank, government agency, etc. using official looking graphics, important-sounding titles and industry jargon to dress-up their messages.
Bridge salesmen and other con artists have been studying human psychology for millennia. Their delivery methods have evolved along with their tactics. Email represents a relatively low cost, low risk way for swindlers to initiate a scam, but it is by no means a low yield enterprise. Tenacious tricksters will continue to infiltrate inboxes, as long as there is a profit to be made. Thus, the onus is on all email users to be aware of what kind of requests their fellow employees, banks, government agencies, post-secondary institutions etc. might reasonably ask them to send electronically, and to be wary of any unusual demands.
Suspicious activity in your GVSD email inbox should be forwarded to spam@sd61.bc.ca as quickly as possible, and if you believe your account may have been compromised please call Helpdesk immediately at: 250-475-4188.


